Facebook FriendFeed Stored XSS

I'm writing about a stored XSS which I found on one of Facebook's Acquisition, FriendFeed.
I started to check on FriendFeed website, for possible bugs, but failed to get anything good there. Then all of a sudden, I thought to give a shot on it's API.
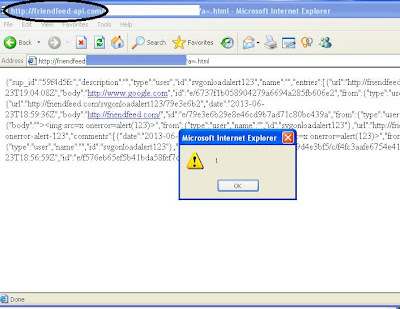
FriendFeed API, allows users to fetch status updates, comments etc. from FriendFeed profiles of any user.So I changed the profile name of my test to an XSS payload, upon viewing the profile via JSON output through the API results in an XSS being triggered (Which initially worked on IE6 :( ).
Whoa, XSS executed? but wait it's executed on friendfeed-api.com, not on friendfeed.com. I reported this to Facebook Security and they said :
Hi Prakhar,
This would execute on friendfeed-api.com, though, not friendfeed.com. Are you able to access session cookies or sensitive information on the other domain?
Thanks,
Rory
Security
So, I started to find a way through, after Googling for some time. I discovered a deprecated version of FriendFeed API, which executed on www.friendfeed.com (of course, not on friendfeed-api.com).
So, I updated my test account's status and then commented an XSS vector on it, fetching the comment will result in a non-sanitised JSON being returned and XSS being triggered via content-sniffing. (Only in IE, upto 9).